-
 chevron_right
chevron_right
Movim 0.29 Rankin, time to share your Story!
Timothée Jaussoin • pubsub.movim.eu / Movim • 1 January 2025 edit • 2 minutes
New year, new #release ! This time with plenty of new exciting features, let's have a look at them. 😊
Stories
The past few years several chat platforms tried to blur the line between their chat and social features.
Stories are a very nice way to share content with your contacts and allow them to react easily by chat.
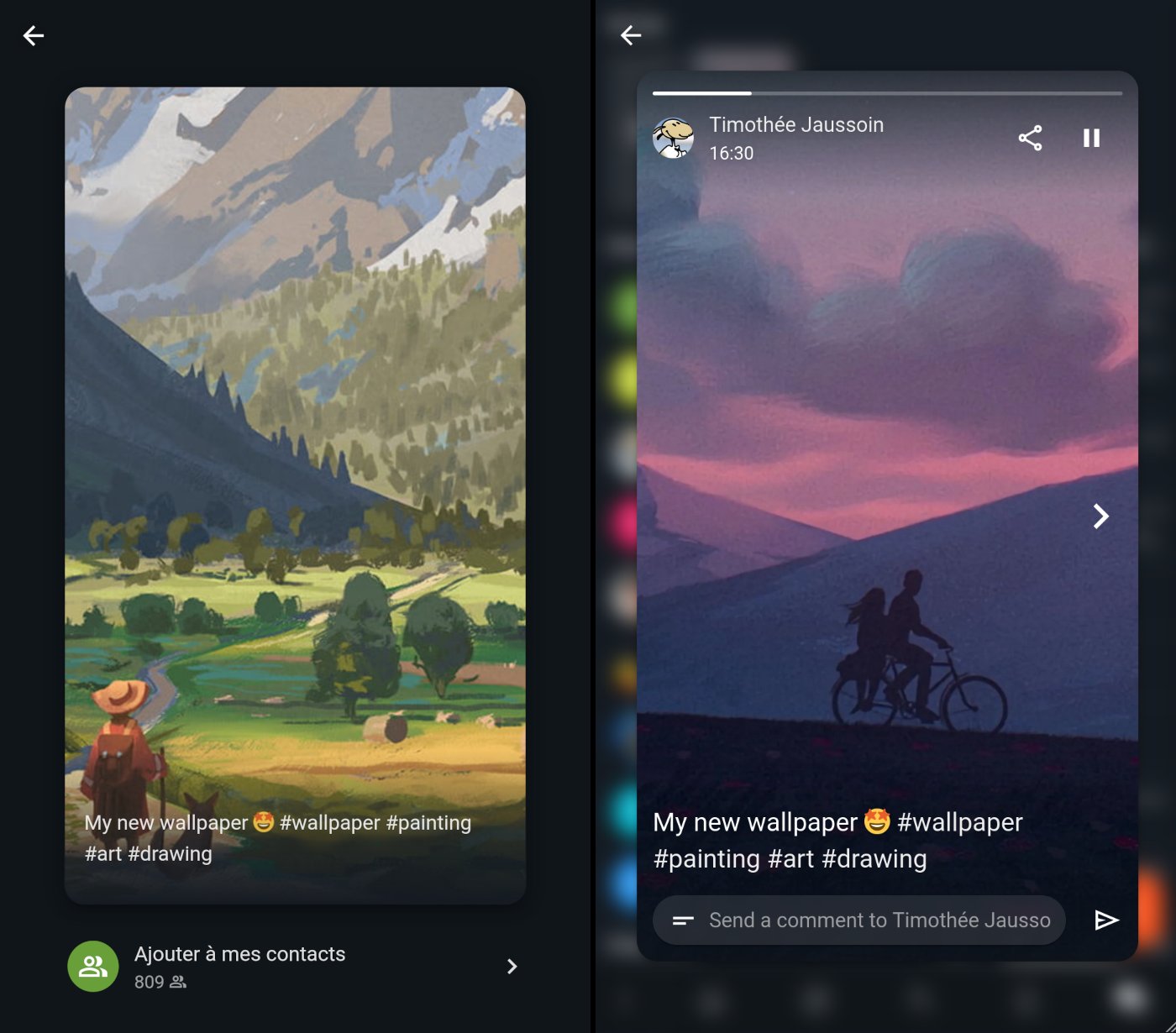
Movim 0.29 is the first XMPP client that implements Stories. A specific XMPP extension, XEP-0501: Pubsub Stories, was created to standardize and allow perfect compatibility with other clients on the network. XMPP is once more showing its capability to be a perfect protocol to build this kind of feature and deploy it easily across a large network of compatible clients.
While writing this article some other XMPP clients are already planning to implement the feature.
You'll be able to create a new Story by taking a picture directly with your camera or select one from your gallery, edit it, add a small text and publish it to your contacts. Your story will then be available for 24 hours, and your contacts will be able to comment on it by sending you a chat message.
In the upcoming versions more features will be progressively added to complete those ones. If you are looking for a feature in particular feel free to drop a comment or a message in the support room. 😌
Briefs
This version is also introducing Briefs, a simpler way to publish content on your profile or in your Communities.
Until now you were invited to write posts having a title and a content. Briefs allows you to directly publish a short text to your contacts like on Mastodon, Twitter or Bluesky. If you feel the need to express yourself in a more "bloggy" way you can always switch back to the complete experience.
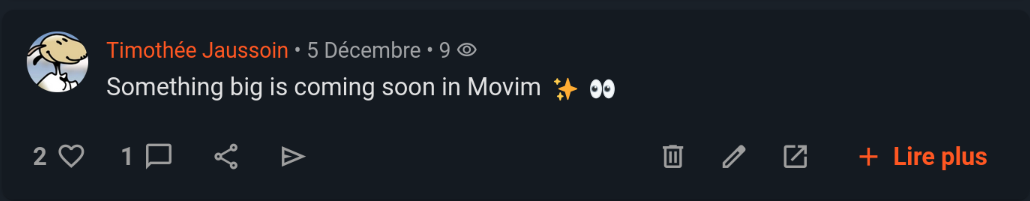
Some refactoring was done in the database and user interface to better integrate Briefs in the feeds.
But also...
An important refactoring was done regarding how the internal dates and times were handled. Now each connected user is sending its own timezone on login and all the times are generated dynamically using those timezones; this solves some weird calculated hours during the switch between daylight saving times.
Lots of fixes were done in how the chat discussions are handled and cached. This is fixing a few erratic behaviors in how chat discussions were ordered and their related notifications displayed.
And as always some database, user interface and JavaScript fixes.
Some news from the Movim Live project
The Phase 2 of the Movim Live project is finally getting in shape. Movim is now able to start and join a multiparticipant call and get their cameras and microphones. This required some important refactorings in how the calls and media streams were handled internaly, you can follow the dedicated branch there Pull Request: Multiparty Jingle.
This second important phase should be finished in a few months and a dedicated version (maybe a 0.30 ?) will be published then.
In the meantime lets enjoy all the new exciting features.
Happy New Year to all the #Movim and #XMPP users 🎉
That's all folks!








