-
To
chevron_right
DISH Sues ‘Pirate’ IPTV Services Lemo and Kemo in U.S. Court
news.movim.eu / TorrentFreak • 8 April 2025 • 3 minutes
 With the continued growth of pirate IPTV services in recent years, TV broadcasters and distributors have been ramping up their anti-piracy efforts.
With the continued growth of pirate IPTV services in recent years, TV broadcasters and distributors have been ramping up their anti-piracy efforts.
The International Broadcaster Coalition Against Piracy ( IBCAP ) has been particularly active. It’s also the main driver behind a new lawsuit filed yesterday by DISH Network at a Texas federal court.
Lemo TV & Kemo IPTV
The American pay-TV provider accuses the operators of popular streaming services ‘Lemo TV’ and ‘Kemo IPTV’ of direct copyright infringement. These services, operating from Lemotv.com and Kemoiptv.com respectively, promise access to “over 18,000 live channels” and “over 8,400 shows” for a fraction of the price of legal subscriptions.
“Defendants offer United States Subscribers a 36-hour free trial to the Service and sell Service Subscriptions for one device for $28.50 for six months, $39 for one year, $59 for two years, and $100 for four years,” the complaint notes.
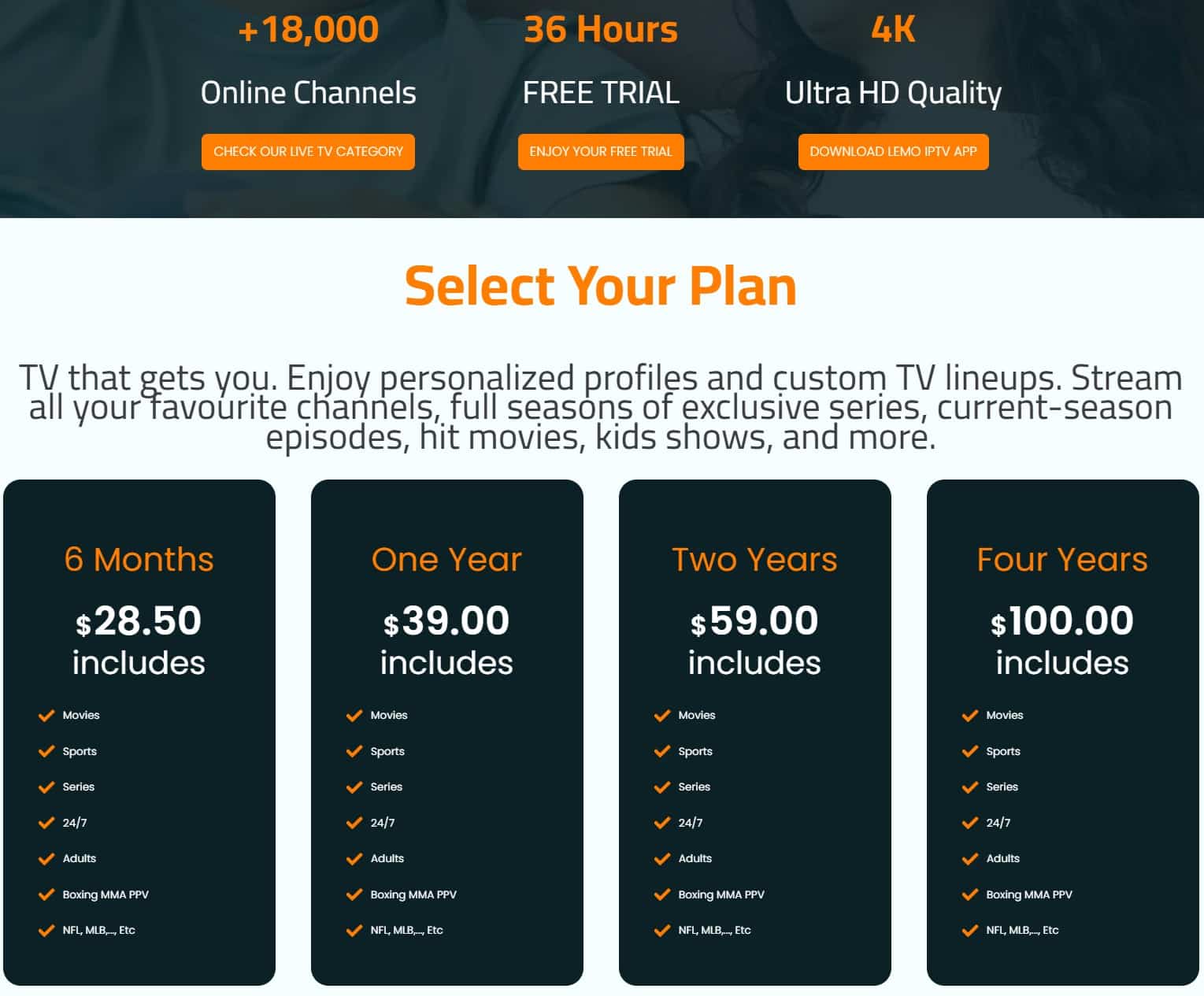
In addition to selling direct to consumers, both services operate reseller programs. This allows third parties to launch their own custom-branded IPTV streaming sites and apps for under $200. Resellers purchase credits for use with their branded services which they can resell to their own customers at a significant markup.
In a footnote, DISH claims that resellers of Lemo TV and Kemo IPTV include the following: Xtremehdiptv.org, Bestusiptv.com, Slingtvbox.com, 1dollariptv.com, Fubo-iptv.com, Tv-wave.com, Kemoiptv.shop, Geministreamz.us, Honeybeetv.com, Honeybeeiptv.org, Honeybeeiptv.io, Dynastyiptv.shop, Dynastyiptv.com, Dynasty-iptv.com, Caliptostreams.com, and 4kliveiptv.com.
Unveiling the John Doe Operators
The complaint alleges Lemo and Kemo use the services of Cloudflare and Namecheap, which are both based in the United States. However, the identities of the operators remain unknown. DISH hopes to uncover more information through this lawsuit so it can name the defendants in an amended complaint.
To gather more information, DISH filed a motion to expedite discovery. Specifically, it seeks permission to subpoena a wide variety of third-party intermediaries who may be able to help identify the defendants.
These include Cloudflare and Namecheap, but also other hosting companies, payment providers, and social media services such as 24 Shells, Des Equity, Hivelocity, Tucows, GoDaddy.com, DigitalOcean, Newfold Digital, Google, Coinbase, PayPal, Meta Platforms, and X Corp.
The discovery request is not limited to the main Lemo and Kemo domains, but also includes the alleged reseller services, as shown below.

$25 Million in Damages
The lawsuit mentions that at least 171 registered copyrighted works were infringed and DISH seeks the maximum of $150,000 in statutory damages for each, totaling over $25 million. In addition, the complaint seeks an injunction to transfer the infringing domain names.
While their identities are currently unknown, DISH believes that the defendants acted willfully and on a massive scale, ignoring approximately 100 notices of infringement sent by IBCAP and DISH since February 2021.
IBCAP executive director Chris Kuelling says that their anti-piracy lab classifies Lemo and Kemo among the most egregious IPTV services. During the first quarter of 2025, the services accounted for nearly 30% of all unauthorized streams detected on set-top box and IPTV services.
Based on this data, IBCAP helps its members to select the prime candidates for legal action, which ultimately resulted in this week’s lawsuit.
“This lawsuit is the latest example of our lab’s ability to identify the pirate services that are significantly infringing our members’ content and stack-rank such services in order to target and remove the worst infringers.”
“This level of theft is unacceptable for our members, and we will put a swift stop to it—just as we have successfully done with numerous other pirate services through court-ordered injunctions,” Kuelling adds.
—
A copy of the DISH Network complaint, filed yesterday at the U.S. District Court for the Southern District of Texas, is available here (pdf)
From: TF , for the latest news on copyright battles, piracy and more.


 Like many similar reports published most weeks by newspapers in Europe, an article published by Belgian media outlet L’Echo late Saturday evening pulled few punches.
Like many similar reports published most weeks by newspapers in Europe, an article published by Belgian media outlet L’Echo late Saturday evening pulled few punches.
 While this would be its first use in Belgium, dynamic blocking is already used extensively elsewhere. The mechanism allows for speedy responses to blocking countermeasures, including domain changes and the appearance of proxies and mirrors, and there’s no requirement for a follow-up legal procedure.
While this would be its first use in Belgium, dynamic blocking is already used extensively elsewhere. The mechanism allows for speedy responses to blocking countermeasures, including domain changes and the appearance of proxies and mirrors, and there’s no requirement for a follow-up legal procedure.
 Most prevalent in the movie and TV show sectors, applications for DMCA subpoenas are regularly filed at courts in the United States.
Most prevalent in the movie and TV show sectors, applications for DMCA subpoenas are regularly filed at courts in the United States.
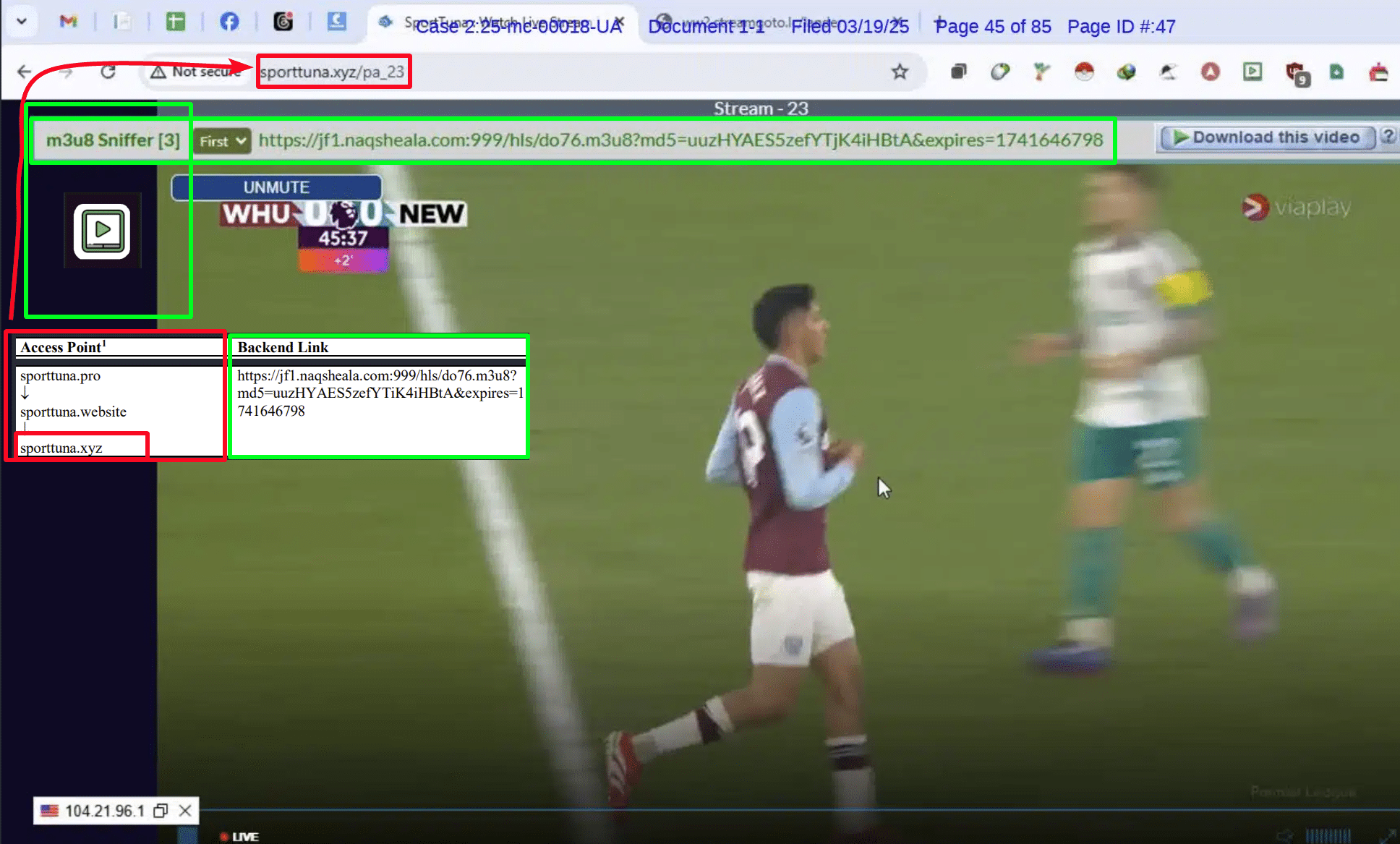
 In this example it appears that when the Premier League visited the website sporttuna.pro, they were redirected to sporttuna.website and then to sporttuna.xyz (boxed in red).
In this example it appears that when the Premier League visited the website sporttuna.pro, they were redirected to sporttuna.website and then to sporttuna.xyz (boxed in red).
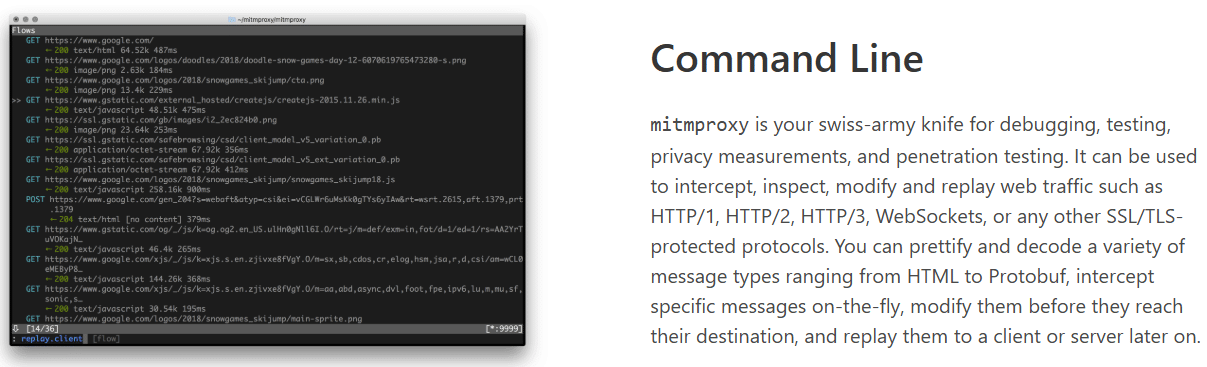
 Identifying the remaining tools was a little time-consuming but if we said the method was advanced or complicated, that would be a lie.
Identifying the remaining tools was a little time-consuming but if we said the method was advanced or complicated, that would be a lie.
 Given that M3U8 Sniffer “does NOT provide functionality to download the actual video streams” another piece of software comes in handy. IDM is a popular choice in the niche and appears to be the downloader of choice in this particular toolkit.
Given that M3U8 Sniffer “does NOT provide functionality to download the actual video streams” another piece of software comes in handy. IDM is a popular choice in the niche and appears to be the downloader of choice in this particular toolkit.
 Our best guess at identifying this next tool comes with a small caveat that its icon was almost impossibly blurred and even when fresh it’s still pretty basic. Ultimately, a green diamond and a single white ‘F’ works here.
Our best guess at identifying this next tool comes with a small caveat that its icon was almost impossibly blurred and even when fresh it’s still pretty basic. Ultimately, a green diamond and a single white ‘F’ works here.
 Scraping data from websites in a structured and usable format isn’t always easy and for big jobs, things can quickly descend into a time-wasting nightmare.
Scraping data from websites in a structured and usable format isn’t always easy and for big jobs, things can quickly descend into a time-wasting nightmare.
 Given that there are Android emulators that are less elaborate, more predictable, and therefore better suited to the assumed job in hand, the discovery of two fairly elaborate emulators in the toolkit initially seems a little puzzling.
Given that there are Android emulators that are less elaborate, more predictable, and therefore better suited to the assumed job in hand, the discovery of two fairly elaborate emulators in the toolkit initially seems a little puzzling.